VPN split tunneling explained quickly:
Split tunneling allows you to route only certain apps or websites through the VPN or prevent them from connecting to a VPN. It’s handy when you want faster speeds at the cost of privacy that the VPN provides. Split tunneling is available in almost all premium VPNs.
It divides traffic into two parts, where one portion is VPN-protected and the other originates from your original IP. Find out more about how it works and how to use it in our in-depth split tunneling VPN guide.
A split tunneling VPN is a VPN service that allows you to select which apps/domains/IPs will or won’t take advantage of a VPN tunnel. This feature is useful for VPN protecting certain “portions” of your traffic while leaving others unaffected by encryption and IP change.
This is usually a premium feature, which can be found in popular VPNs like ExpressVPN, NordVPN, and even CyberGhost. However, split tunneling can be divided into several categories. Plus, it has a few specific use cases that we’ll go over in this Split Tunneling VPN guide.
What Is Split Tunneling? How Does VPN Split Tunneling Work?
Full tunneling is when you connect to a VPN and all your traffic is routed through an encrypted tunnel. Conversely, split tunneling is when only specific apps or domains use an encrypted tunnel. This allows for more control over which data you want to anonymize and which to leave unencrypted.
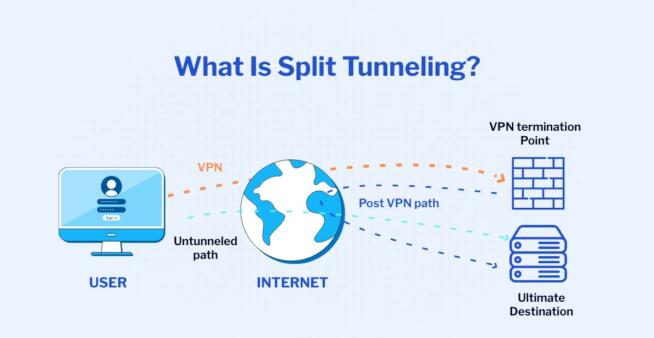
Courtesy of DataProt
Split tunneling essentially gives you two connections. On one hand, you have apps that can go online unencrypted, with your original IP address. On the other, you have VPN-protected apps that use a VPN-given IP address, encryption, and other security measures of the VPN service.
In doing so, you can VPN-protect sensitive data on one side, while on the other, going online without potential speed decreases that VPNs can sometimes produce.
When Should I Use a Split Tunneling VPN?
This brings up the subject of when to use a split tunneling VPN. Obviously, you shouldn’t use it all the time because some online activities practically require the security of a VPN. Below, we examine the cases in which split tunneling will be welcome.
- If you don’t intend to play on distant gaming servers and want to preserve your connection speed, using split tunneling is smart. In this case, you can exclude the game you’re playing from the tunneling process and leave it unaffected by the VPN. This way, you’ll minimize latency and be able to enjoy an impeccable gaming experience.
- Online shopping. When shopping online, especially on local sites, you want to have your original location available. Besides, a local shopping site might not work with an IP from another country, which is why you should use split tunneling and prevent the site from using a VPN.
- Online banking. This one’s important! Local bank sites will NOT work with a foreign IP and in many cases, they’ll detect spam, potentially locking you out of your account. You’ll then need to call the bank, explain the mishap, and waste time on getting back your access. With a split tunneling VPN, your online banking app won’t be affected by the VPN, thus, preventing such annoyances from happening.
Split Tunneling Types Explained
We mentioned that split tunneling comes in multiple variants but the key is that all of them work the same. They either allow or prevent an app/website from using a VPN. There are 3 types of VPN split tunneling, all of which are explained below.
- App Split Tunneling. This type allows you to select which apps will or won’t use a VPN. It’s the most common type that you can find in ExpressVPN or NordVPN.
- Website Split Tunneling. This one works the same but instead of apps, you can choose which domains/URLs will take advantage of a VPN. It’s less common but providers like NordVPN and CyberGhost offer it, along with a few VPN browser extensions.
- Inverse Split Tunneling. As the name implies, it’s the opposite of “normal” split tunneling. Usually, you’ll choose apps and websites that will use the VPN but in Inverse Split Tunneling, everything is routed through the VPN unless you specify apps/sites that won’t use the VPN.
Is Split Tunneling Completely Safe to Use?
The safest way to use a VPN is to tunnel all your traffic and encrypt it. This way, every bit of ongoing and inbound traffic is unreadable by your ISP and can’t be intercepted. Using a VPN split tunneling isn’t ideal, as you’re encrypting a portion of the traffic, while the rest remains unencrypted.
Essentially, it all boils down to compromises and priorities. If you want to prioritize performance and don’t care about privacy for a specific need, using split tunneling is likely going to benefit you. However, when you need to transfer sensitive data and need extra security, split tunneling isn’t the best option.
We must clarify that using split tunneling is still safer than not using a VPN and leaving the entire traffic unencrypted. Besides, high-quality VPNs like NordVPN or ExpressVPN usually don’t slow down your connection, especially when using a server near your physical location.
That said, split tunneling might not be needed unless you use a local service that works only in your country and you don’t want to change your IP.
How to Use VPN Split Tunneling?
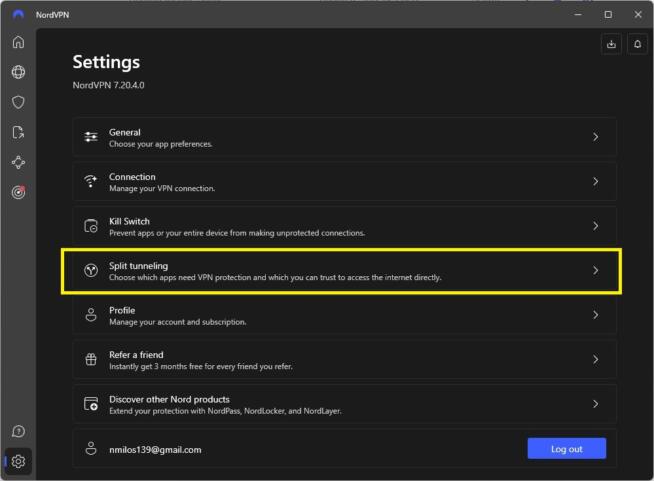
To use split tunneling, you must have a provider that supports it. For this guide, we’ll use NordVPN because it offers split tunneling on multiple platforms. Rest assured, the process is identical to any other split-tunneling-friendly VPN.
- Open NordVPN (or any other VPN).
- Go to Settings.
- Click on Split Tunneling.
- Enable Split Tunneling by using the button displayed in the screenshot.
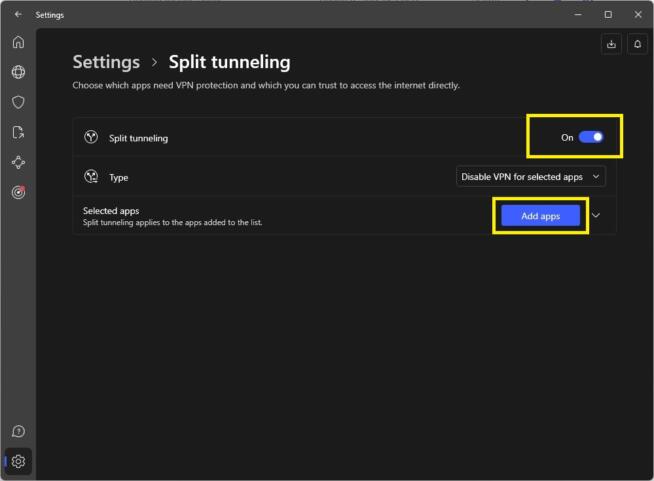
- Under “Type”, select whether you want to disable or enable the VPN for selected apps.
- Under “Selected Apps”, click on “Add Apps” to add applications that will or won’t use a VPN.
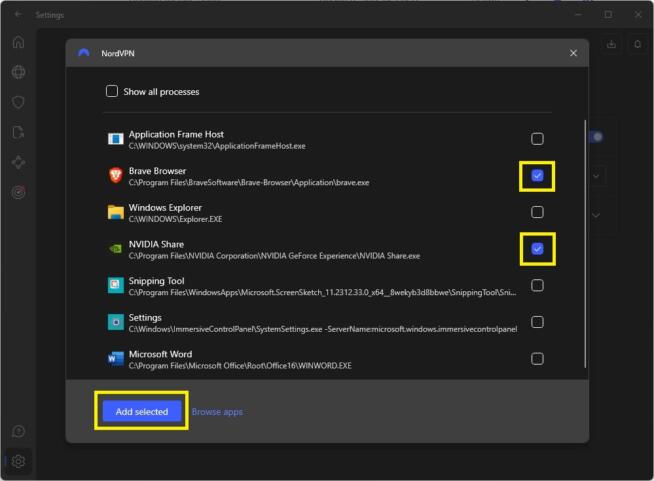
- In the new window, select the apps you want and click on “Add Selected.”
Summary
Split tunneling is immensely useful for preventing or allowing only certain apps/websites to use a VPN tunnel. However, the feature isn’t necessary and is handy only in specific situations where you want to prioritize performance over security or have your native IP visible when using a local site/service.
If you’re looking for a great split-tunneling VPN, our recommendations are NordVPN, ExpressVPN, CyberGhost, and ProtonVPN.
We earn commissions using affiliate links.


![5 Best Instagram Bots [year] (for Followers That Still Work) best instagram bots 2024](https://www.privateproxyguide.com/wp-content/uploads/2021/03/best-instagram-bots-2021-3-150x150.jpg)




![List of VPN Port Numbers Used for VPN Protocols List of VPN Port Numbers Used for VPN Protocols [Guide]](https://www.privateproxyguide.com/wp-content/uploads/2020/10/List-of-VPN-Port-Numbers-150x150.jpg)
![5 Best VPN Providers ([year]) [PC, iOS, Android] VPN](https://www.privateproxyguide.com/wp-content/uploads/2021/03/vpn-150x150.jpg)
![Best VPN for Kodi in [month] [year] Best VPNs for Kodi 2021 - To Avoid Buffering & Other Issues](https://www.privateproxyguide.com/wp-content/uploads/2018/05/kodi-launch-logo-150x150.jpg)
![CyberGhost VPN Review in [month] [year] cyberghost vpn](https://www.privateproxyguide.com/wp-content/uploads/2021/03/cyberghost-vpn-150x150.jpg)
![HideMyAss VPN Review in [month] [year] HideMyAss VPN Review 2021](https://www.privateproxyguide.com/wp-content/uploads/2018/06/hide-my-ass-review-homepage-150x150.jpg)

![How to Check if Your VPN is Working in [month] [year] How to Check if Your VPN is Working in 2021](https://www.privateproxyguide.com/wp-content/uploads/2018/07/How-to-Check-if-your-VPN-Connection-is-Secure-150x150.jpg)
