The easiest way to access the dark web safely on Android is to use the TOR network which can be accessed via special apps. Let’s look closer at what TOR is.
TOR is a decentralized system of proxy servers, where each participant can act as a server and a client: by connecting to TOR from your device, you will automatically establish a connection to a chain of other similar devices (both computers and mobile devices can do this). By opening any site, your traffic passes through a chain of devices and gets encrypted. This enables anonymous surfing, combined with access to special .onion sites. TOR is very similar to the usual VPN services, but it works on much more complex principles and algorithms.
Allowing you to access any information blocked on the Internet that is actively used by journalists and webmasters, it gives one of the greatest benefits, access to .onion sites. These sites are almost impossible to track and even more so to block. In addition, for maximum anonymity and security, we recommend using TOR with VPN!
NOTE: Use a VPN to encrypt your traffic for maximum security to stay safe on the Dark Web.
| VPN Service |
|---|
 www.nordvpn.com NordVPN Review |
| Price: Servers: 5500+ in 59 countries Simultaneous connections: 6 Jurisdiction: Panama Payment: PayPal, AmazonPay, Crypto, Google Pay, Klarna Torrenting: OK Unblocks US Netflix: Yes Dedicated IP: $70/yr TrustPilot Score: 4,7/5 Money-back: 30 days Extra: Double VPN, Obfuscated servers Visit NordVPN » |
| www.expressvpn.com ExpressVPN Review |
| Price: Servers: 3300+ in 94 countries Simultaneous connections: 5 Jurisdiction: British Virgin Islands Payment: PayPal, Crypto, AliPay, Klarna, Torrenting: OK Unblocks US Netflix: Yes Dedicated IP: Not provided TrustPilot Score: 4,7/5 Money-back: 30 days Visit ExpressVPN » |
 www.cyberghostvpn.com CyberGhost Review |
| Price: Servers: 6600+ in 89 coutrines Simultaneous connections: 7 Jurisdiction: Romania Payment: PayPal, Crypto Torrenting: OK Unblocks US Netflix: Yes Dedicated IP: $51/yr TrustPilot Score: 4,8/5 Money-back: 45 days Visit CyberGhost » |
 www.surfshark.com Surfshark |
| Price: Servers: 3200+ in 65 coutrines Simultaneous connections: Unlimited Jurisdiction: British Virgin Islands Payment: PayPal, Crypto, Google Pay, Amazon Pay Torrenting: OK Unblocks US Netflix: Yes Dedicated IP: Not provided TrustPilot Score: 4,3/5 Money-back: 30 days Visit Surfshark » |
 www.purevpn.com PureVPN Review |
| Price: Servers: 6500+ in 140 coutrines Simultaneous connections: 10 Jurisdiction: Hong Kong Payment: PayPal, Credit Cards Torrenting: OK Unblocks US Netflix: Yes Dedicated IP: $35.88/yr TrustPilot Score: 4,7/5 Money-back: 31 days Visit PureVPN » |
Accessing TOR on Android
The best way to access TOR on your Android device is to use special programs. There are several possible options: the official TOR Browser and Orbot + Orfox. While the TOR browser is a self-sufficient application, Orbot and Orfox are not able to work without each other. Let’s look at these options closely.
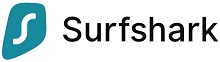
- TOR Browser for Android is a fully-featured browser that combines both repeater and browser features. It allows visiting the usual site as well as .onion sites. You can download it from Google Play or the TOR project download page.
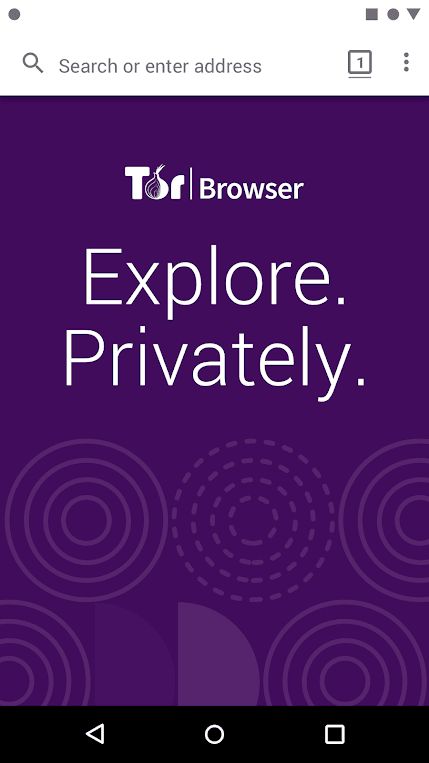
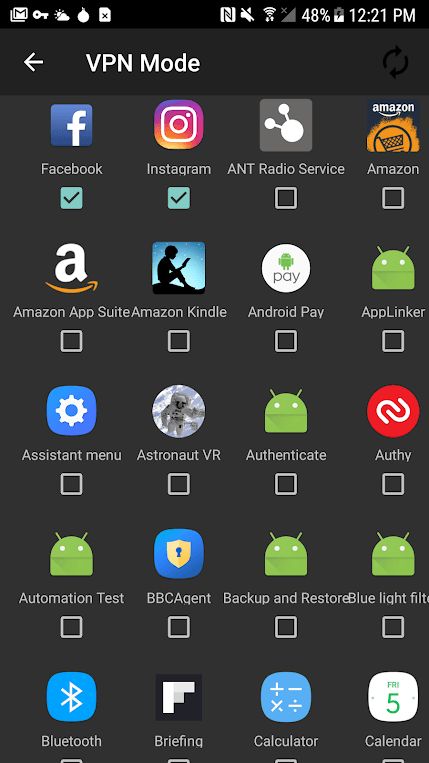
- Orbot: Proxy with TOR. This is a repeater client which allows choosing the apps to work with the TOR protocol. You can download it from Google Play or official sites.
How to Setup TOR on Android?
- Download the TOR browser or Orfox and install them on your smartphone or tablet.
- If you have a TOR browser, the first time you start the application, you will see a repeater window with a button in the middle of the screen. Click on the bulb and press the VPN switch below.
- Now, you just need to enter the address of the website you want. It can be quite difficult to enter the address manually as they have an unusual format so you may want to use the default DuckDuckGo search engine to find the necessary resource.
- If you install Orbot, start it, select the apps to protect and run VPN. Use the apps as usual.
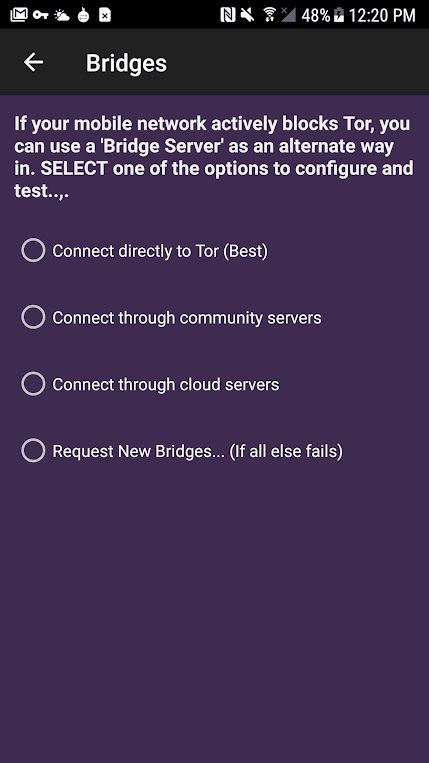
If you can’t connect to TOR from your smartphone, you’ll have to use “bridges”. Most likely, your provider has blocked the standard TOR protocol but by using bridges you can still establish a connection. To do this, go to Settings and tick Use bridges (Orbot) or Internet is censored here (TOR Browser).
Some security advice
- Before using the Dark Web, we recommend you to check if everything went well: to do this, check whether your IP address has changed through. There are a lot of websites allowing you to check your IP address and basic info about your connection. Whoer.net is one the best. Check your IP before and after connecting to the TOR. If the IP and the country have changed, everything is ok and you can proceed.
- There is nothing perfect in this world, everything can be hacked and tracked. If someone really needs to find you, they will be able to track you one way or another. In this case, TOR is not a panacea. Therefore, we recommend that you use TOR together with VPN services to avoid any problems.
- To search for sites, only use the DuckDuckGo search engine, which, unlike Google, Bing, Yahoo! and the like, does not track you or reveal your anonymity.
- Don’t use your main email address on the device where you use TOR regularly. There is a high risk for it to be tracked.
- Don’t use TOR to download torrents from your Android device, it’s best to use a VPN to do so. Firstly, the network is not designed for this format of data transmission, secondly, 99% of repeaters will be forced to block this option. And thirdly, even in ideal conditions, you won’t get speeds faster than 10-15kbps.
- By default, TOR Browser and Orfox have a useful HTTPS Everywhere extension built-in, forcing all connections to use the HTTPS protocol which ensures that your connection is encrypted and protected from data hijacking. If you see a warning when you visit the site that it is unavailable via HTTPS, leave it, because you can be tracked through it.
We hope this material helped you to understand what the Dark Web really is and how to safely use it on Android. Always be attentive and remain secure.
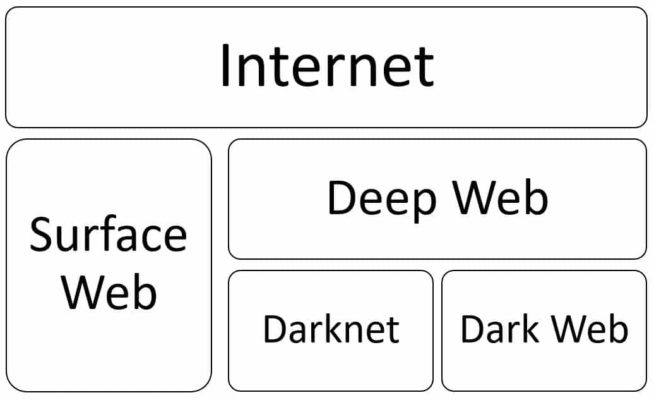
Comparison of Deep Web, Darknet and Dark Web and how they differ from the Clearnet
Imagine a huge iceberg. The top part which is above the water is only a small part of the whole ice block, the largest part is underwater. The same can be said about the Internet. All the pages stored on servers connected to the worldwide network are divided into two main segments: open and hidden. The open segment is usually called the Clearnet or Surface Web. The hidden one is described by three terms, the Deep Web, the Darknet, and the Dark Web. What are the differences between all of them? In many publications, they are often confused so it is necessary to define them correctly.
Firstly, let us look closer at the Clearnet also known as Surface Web. What is it? In short, it is the Internet we use every day. Technically, it is the World Wide Web of all resources accessible from the Internet without special software like a dark web browser and configuration. It contains all the well-known websites which can be found through Google or any other search engine. These websites can be social media, news sites, weather forecasts, online banking, magazines and newspapers, cloud storage, and many others.
To access them, you don’t need to know the exact web address. Yes, knowing it will save much of your time but you can search the address using certain keywords. In most cases, every search engine will give you even millions of results. This shows that there are a lot of web pages existing online in the Clearnet. According to some statistics, the number reaches about 1 billion pages available worldwide.
The next segment of the Internet is the Deep Web. What is that? This is the segment of the Internet that is not indexed by any search engine. What does this mean for you? This means that you cannot access that web page through a search engine. The Deep Web contains a huge number of web pages, databases, special forums, and many other resources. You will have to know the exact address or have a direct link but you do not need any special settings or software to get access to these websites. These web resources are correctly directed by normal DNS.
However, in some cases, you may require special software.
For which type of content would that be the case? It can be anything that requires special permissions or passwords, or some private information, which cannot be shown to everyone. These resources can include closed corporate networks, premium content, archives, document storages, special forums, medical resources, government portals, police reports, financial management systems, email accounts, and many others. Even Netflix is some form of Deep Web because you cannot access it without a subscription. Information can be hidden for any reason and it does not mean it is always illegal. In most cases, it is legal, it is just secret and not everyone is permitted to view it.
The Darknet is an overlay network, which requires special software, tools or configuration to access it. It is more known to most people because it is used worldwide. Physically, it uses the Clearnet infrastructure but it can be compared to a virtual network with a special configuration. You cannot access it with a normal browser like Google Chrome or Mozilla Firefox using a standard configuration of your ISP. Any encrypted network unavailable through a search engine and requiring a special software can be considered to be part of the Darknet. In most cases, it is encrypted by different protocols and that is why it provides great anonymity to its users. The most known Darknet networks are various friend-to-friend networks like I2P, Freenet, various torrent trackers working through the BitTorrent protocol and TOR network for anonymous access to both normal Internet and special hidden resources.
For example, let’s look at the TOR network. It uses a special configuration, which is not compatible with standard DNS, protocols, and routings. It uses the so-called Onion routing, which does not exchange any information exchange between two connected computers. Each computer used as a part of the network is configured and encrypted the same way as the others. Using Tor, you can access any Surface Web resources in the world as well as the hidden ones, which are encrypted to be accessed only via Tor. Such hidden resources use the .onion domain and are accessible only through the TOR browser or special proxy. That is why the TOR network is often called Onionland.
The Dark Web is the World Wide Web of the Darknet. It is a small part of the Deep Web and includes all overlay networks, which use the Internet for their work but are accessible only through special software and tools. While the Darknet is one specific network, the Dark Web is the global network of all the Darknets. It functions as the surface web but is completely controlled by the users of the Dark Web. Like the Dark Net, the Dark Web cannot be accessed through search engines and traditional software. You have to know the exact address and have their special software. Very often, it is confused with the Darknet and is often used as an interchangeable term.
What is the Dark Web used for and why you may want to access it?
As we described earlier, the Deep Web is used to hide some content so that it is not easily accessible to all internet users. However, what about the Darknet? How is it mostly used?
As the Darknet is highly encrypted and secure, it is very often used by criminals to commit illegal activities. In most cases, it is impossible to track the origin of these resources so no one can be punished. Some of the users sell drugs and firearms or distribute child pornography. Terrorists can plan their attacks or hackers distribute dangerous viruses or malicious software. Any fraud can buy stolen IDs and passwords to your online banking or launder money. On some resources, black transplantologists can get orders for human organs and kidnappers or traffickers can discuss their next victim.
Nevertheless, is the use of the Darknet always related to crimes? In some totalitarian countries where the Internet is censored and many anti-government resources are blocked, many freedom fighters can use the Darknet to post their messages. To fight against these political regimes there is no other way but to use the Darknet.
As you can see, it can be very dangerous to use Darknet resources. So why may you want or need to access them?
If you live in a country where the Internet is very limited and censored, sometimes there is no other way to communicate with the outside world. For example, to access some forbidden websites like Facebook, Twitter or YouTube, you can use the dark web browser. You will remain anonymous and the cyber police will not catch you.
Also, you may want to check if someone spread your stolen financial information, credit card number or ID card or if traffickers or kidnappers are tracking you. Of course, it is better to hire a skilled professional who can find all this information for you, but if for any reason you cannot do that, you may want to try it yourself.
Nowadays many people are anxious about their private information being collected and stored by the government. Not everyone is comfortable with that so they decide to use encrypted networks like Tor.
We earn commissions using affiliate links.





![How to Safely Buy Bitcoin with PayPal: Complete Guide [year] How to Buy Bitcoins with PayPal](https://www.privateproxyguide.com/wp-content/uploads/2023/02/How-to-Buy-Bitcoins-with-PayPal-150x150.jpg)
![Best SEO Proxy Providers [year]: Boost Your Rankings Safely Best SEO Proxy Providers](https://www.privateproxyguide.com/wp-content/uploads/2023/05/Best-SEO-Proxy-Providers-150x150.jpg)
![Best Web Hosting for Small Businesses to Grow Online [year] Best web hosting for small business](https://www.privateproxyguide.com/wp-content/uploads/2022/03/Best-web-hosting-for-small-business-150x150.jpg)

![Best Web Scraping Tools [year]: Top Picks for Data Extraction Best Web Scraping Tools](https://www.privateproxyguide.com/wp-content/uploads/2022/11/Best-Web-Scraping-Tools-150x150.jpg)
![SOAX Review: Top Proxy and Web Scraping Solutions for [year] soax](https://www.privateproxyguide.com/wp-content/uploads/2024/05/soax-150x150.jpg)




Using TOR, Orbit, Orfox or onion can access a facebook or youtube account???